DNSSEC Technology
DNSSEC is a security extension to the DNS system. It provides an authentication mechanism between DNS servers and validates each DNS zone to ensure data integrity.
1. Introduction to DNSSEC
The traditional DNS protocol provides no mechanism for authenticating the source of DNS data. Facing risks such as DNS spoofing or data tampering during interactions between DNS servers, resolvers, and forwarders, the DNS Security Extensions (DNSSEC) were developed and deployed to protect DNS against data spoofing and manipulation.
DNSSEC provides an authentication mechanism between DNS servers and cryptographically validates each DNS zone to ensure data integrity.
As an extension to DNS, DNSSEC introduces mechanisms that authenticate and protect the integrity of DNS data. DNSSEC adds four new DNS record types:
DNSKEY (DNS Public Key): Used to authenticate the zone.
RRSIG (Resource Record Signature): Digital signatures used to authenticate DNS resource records.
NSEC (Next Secure): Used for authenticated denial of existence for DNS records, combined with RRSIG to validate the zone.
DS (Delegation Signer): Used to establish the chain of trust between parent and child zones.
The objective of DNSSEC is to preserve the standard DNS data flow and delegation process from parent to child zones, while requiring resolvers to support DNSSEC validation. A signed DNS zone includes DNSSEC-related records such as RRSIG, DNSKEY, NSEC, and DS.
By introducing new DNS record types and enhanced validation procedures, DNSSEC extends DNS with strong security features, ensuring authenticity and integrity of DNS data. It supports traditional DNS operations while strengthening reliability, security, and resilience of the Vietnam National Domain Name Server System.
On October 23, 2014, the Ministry of Information and Communications issued Decision No. 1524/QĐ-BTTTT approving the national DNSSEC deployment plan for the “.vn” TLD. The decision defines objectives, scope, and deployment phases of DNSSEC in Vietnam, structured into three main stages.
Uniform implementation of DNSSEC on the national “.vn” DNS system ensures accuracy and trustworthiness of “.vn” domain usage on the Internet, establishes DNSSEC-compliant interoperability between the Vietnam National Domain Name Server System, the DNS root zone, and other global DNS systems, and marks a significant milestone in the development of Vietnam’s Internet infrastructure.
DNSSEC deployment in Vietnam follows a step-by-step approach, beginning with the national “.vn” DNS servers, and expanding to second-level shared domains (e.g., gov.vn, net.vn), DNS systems of ISPs, registrars, DNS hosting providers, government agencies, and holders of “.vn” domain names.
2. DNSSEC Application for Securing DNS Systems
DNSSEC records are published in DNS zones to authenticate the information within those zones, ensuring trustworthiness of DNS exchanges and queries. While traditional DNS resource records continue operating normally, DNSSEC records must be correctly configured and cryptographically synchronized.
DNSSEC introduces the concept of Zone Signing, which includes DNSKEY, RRSIG, NSEC, and DS records. A zone lacking these records is considered unsigned. DNSSEC also requires modifications to the CNAME definition by introducing corresponding RRSIG and NSEC records.
Adding DNSKEY Records to a Zone
To sign a zone, the administrator generates one or more public/private key pairs—typically a Zone Signing Key (ZSK) and a Key Signing Key (KSK). The corresponding DNSKEY records are added to the zone and the private keys are used to generate RRSIG signatures.
The DNSKEY record must have the Zone Key flag set to 1. A signed zone must contain at least one DNSKEY acting as its trust anchor, which pairs with its corresponding DS record stored in the parent zone as part of the DNS delegation chain.
Adding RRSIG Records to a Zone
Once the DNSKEY is in place, all DNS resource records in the zone must be signed, generating RRSIG records. A resource record may have multiple associated RRSIGs.
RRSIG records contain cryptographic signatures that validate their associated resource records. Their TTL may differ from the base TTL of the original record.
Where a domain name owns multiple resource record types, validation requires both RRSIG and NSEC records. This also applies to CNAME records.
NS record sets must also be signed, especially when part of a delegation from parent to child zones. Glue records must also be signed.
Adding NSEC Records to a Zone
Each domain name that owns more than one RRset or participates in delegation requires an NSEC record. The minimum TTL of an NSEC record must match the zone’s SOA minimum TTL.
RRSIG and NSEC records together ensure authenticated denial of existence. No RRSIG or NSEC records are created for domain names that have no resource records before signing, to maintain consistency between signed and unsigned space and avoid validation anomalies.
NSEC records appear at domain names owning RRsets and at delegation points, and all NSEC records must have corresponding RRSIG records.
Adding DS Records to a Zone
DS records establish authentication between parent and child zones. A DS record is created when a signed child zone is delegated. DS records in the parent zone combine with RRSIG signatures to validate the child zone’s authenticity.
The TTL of DS RRsets must match the TTL of the corresponding NS delegation RRset. Creating a DS record requires knowledge of the child zone’s DNSKEY to maintain the DNSSEC chain of trust.
Changes to CNAME Records
When a CNAME exists at a domain name in a signed zone, it must coexist with RRSIG and NSEC records. While the original CNAME specification did not allow coexistence with any other record type, DNSSEC modifies this rule to allow CNAMEs to coexist with their required RRSIG and NSEC records.
Overall DNSSEC Validation Purpose
DNSKEY: Provides the public key used for authenticating DNS servers and zone data.
RRSIG: Signs resource records such as SOA, A, MX, etc.
NSEC + RRSIG: Authenticates NS records and provides authenticated denial of existence.
DS + RRSIG: Validates delegation from parent to child zones.
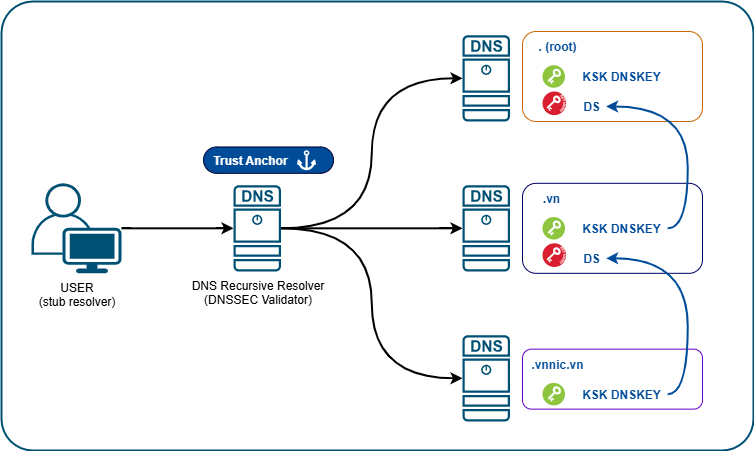
DNSSEC ensures zone data authenticity and integrity by building a cryptographic chain of trust throughout the DNS hierarchy.
3. DNSSEC Deployment
DNSSEC Deployment Process
The DNSSEC deployment process includes:
Establishing DNSSEC-enabled delegation for the “.vn” domain from the DNS Root to the national DNS servers, and
Signing and delegating DNSSEC-enabled child zones from the Vietnam National Domain Name Server System to subordinate entities.
DNSSEC deployment on the national “.vn” DNS system consists of the following steps:
On the DNS Server:
Step 1: Generate public/private key pairs
Step 2: Securely store private keys
Step 3: Publish and distribute public keys
Step 4: Sign the DNS zone
Step 5: Perform key rollover
Step 6: Re-sign the zone
On the Resolver:
Step 7: Configure Trust Anchors
Step 8: Establish the chain of trust and validate DNSSEC signatures

